A few years ago, while I was leading security initiatives at a fast-growing fintech, the regulator decided to conduct an inspection, what most people would formally call an audit. All hell broke loose, most of the team came from an e-commerce background, where regulatory audits were rare, if not completely unheard of.
Questions started flying almost immediately. What exactly is an audit? What will they ask? Do we need to generate evidence? How strict are auditors? What’s the flow of the inspection?
During one of our internal audit discussions, someone from the engineering team casually referred to the auditor as “the dude.” The auditor, quite rightly, responded with: “Please use parliamentary language” 😀
That moment stuck with me and became the trigger for documenting a set of very practical do’s and don’ts. We eventually navigated the inspection successfully. I spent a good amount of time guiding engineers, articulating the process, and helping everyone stay calm, prepared, and professional.
I was reminded of that experience recently when a client found themselves in a very similar situation: first audit, regulated environment, and a lot of nervous energy. That’s what led me to put together this survival guide.
Any Senior engineer working in a fintech company would face an Audit at some point in their career. Audits don’t just involve leadership; engineers, admins, and team leads are often pulled in to explain systems, controls, and evidence. If you’re facing your first audit, I hope this helps you approach it with a bit more confidence (and fewer surprises).
1. Professional Conduct (Non-Negotiable)
- Be formal and respectful. Address auditors as Sir/Madam.
- Avoid casual language like bro, dude, or inside jokes—even with colleagues.
- Remember: everything said in an audit meeting is effectively “on record”.
2. How to Answer Questions
- Answer only what is asked, no extra context unless requested.
- Keep responses clear, factual, and concise.
- If unsure, say: “I’ll check and get back with a confirmed answer.”
- Never guess, assume, or improvise.
3. Use the Audit Anchor
- There is usually a designated audit point-of-contact from the company side.
- Route clarifications, follow-ups, or concerns through this person via a separate channel.
- Do not attempt to “negotiate” or over-explain directly with auditors.
4. Stay Calm (Even When It’s Painful)
- Some auditors deeply understand systems; some don’t.
- Repetitive or irrelevant questions are part of the job and don’t take them personally.
- Frustration or irritation only creates more scrutiny.
5. Evidence: Quality > Quantity
- Share only the evidence requested and nothing more.
- Verify accuracy before submitting (wrong evidence causes more questions).
- Prefer PDF format for all evidence.
- Name files clearly and consistently.
6. Documentation Is Your Shield
- Document your work as you build—not just for audits.
- Good documentation reduces explanations, meetings, and follow-ups.
- If it’s not documented, assume you’ll have to explain it later.
7. Screen Sharing: Handle with Care
- Never share your entire screen on Zoom, Google Meet, etc.
- Always share only the specific application window needed.
- Double-check for sensitive tabs, terminals, or notifications before sharing.
8. Sensitive Data: Stop and Escalate
For any of the following, do not share directly:
- Database screenshots
- PII or customer data
- Passwords, secrets, tokens
Always get approval from: Your Manager, InfoSec and/or Legal teams.
Final Rule of Thumb
Be precise. Be calm. Be professional.
Audits are about evidence and clarity and not speed or bravado.
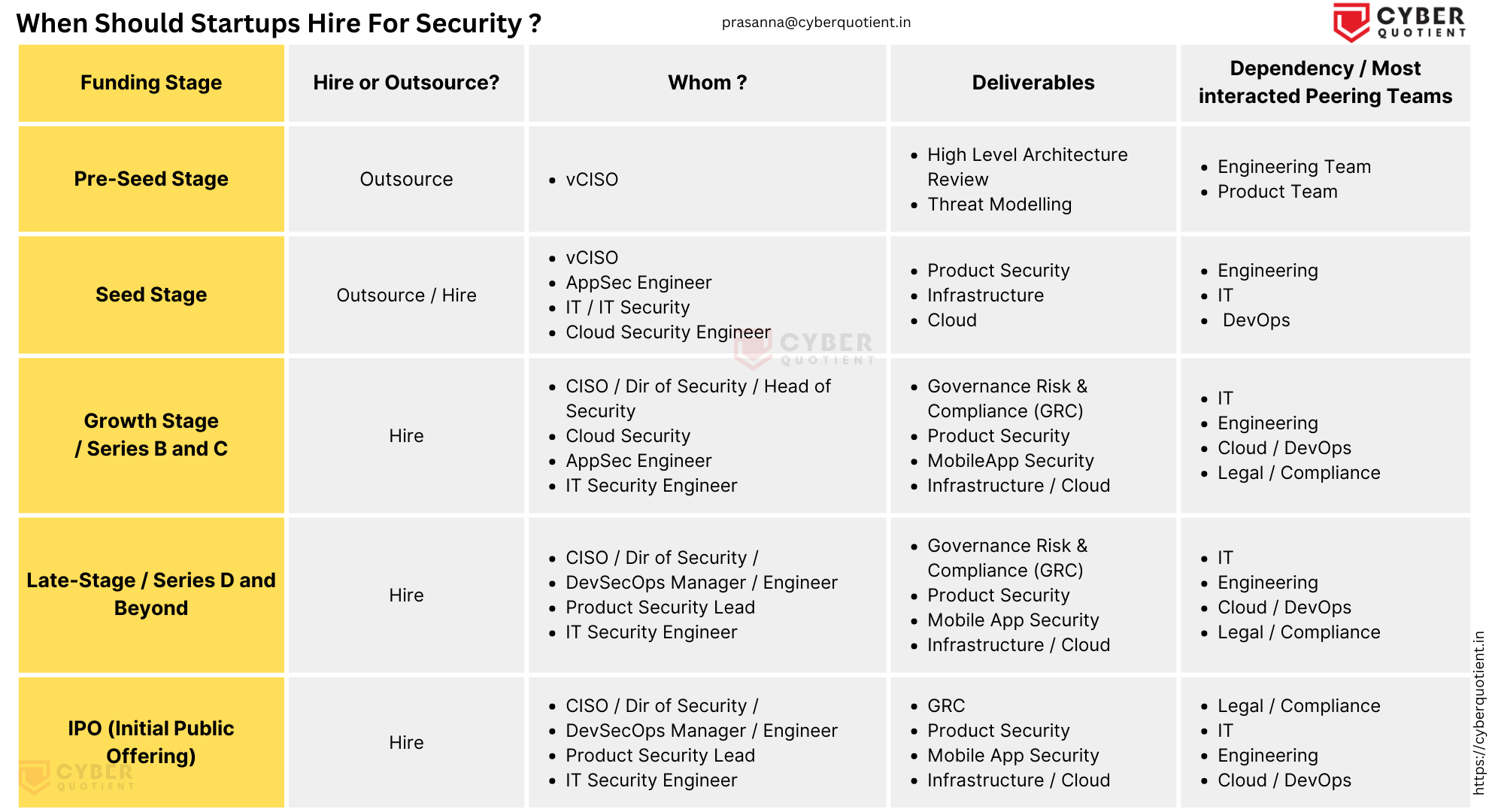
You might also be interested in reading about Audit Fatigue