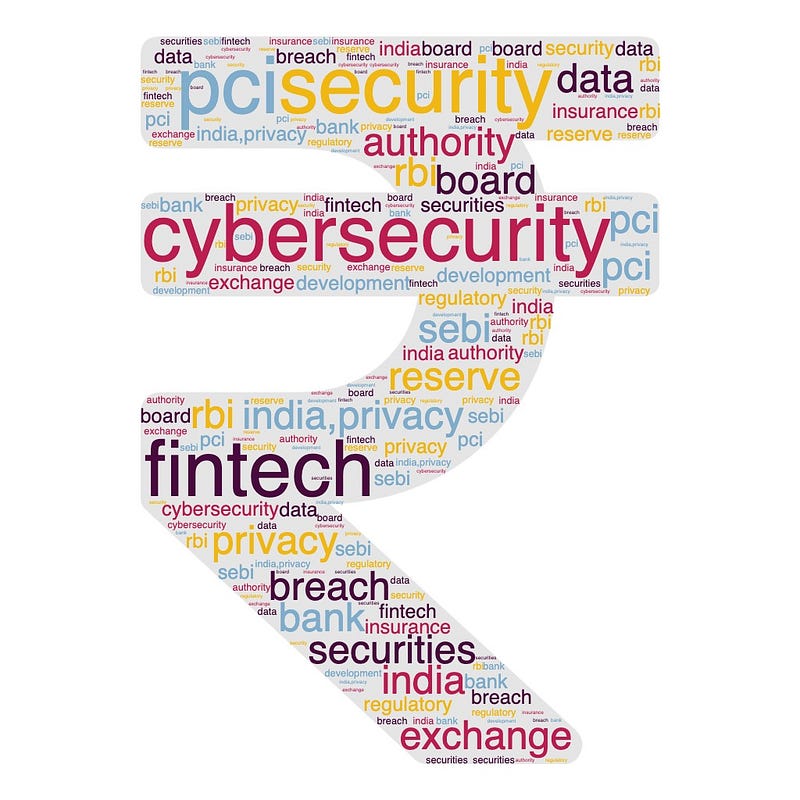
October, as we all know, was celebrated as National Cyber Security Awareness Month. While it is good to emphasize the importance of security with a month dedicated to it, Security Awareness is an ongoing activity.
According to this survey, only 45% of the participants said their employer offers formal cybersecurity training.
Remember that our teams and employees need to be aware of security best practices all around the year and not just for a month. A hacker needs one successful chance while we need to be right 100 % of the time, 365 days a year.
Over years I have conducted numerous workshops and awareness sessions for employees as part of induction, periodic training, sent countless emails & presentations, and conducted phishing simulations. However, it is difficult to hold attention for longer periods and them to be aware of the threats all the time. I think that there is fatigue associated with the traditional way of sending presentations, forcing wallpapers, screensavers, and email blasts.
Most people usually relate to movies, books, songs and other visual content better than usual presentation slides. In addition to existing modes, you can plan to have movie streaming or a book reading activities as a monthly or quarterly event and integrate them with ongoing company events/town halls.
During the COVID days, one of our HR organised monthly book reading events on zoom and it was a big hit. We would pick a chapter and read and review it. It also brought lot of people together!
Screen a movie in your office cafeteria, give out some goodies and swags for those who turn up or throw in a simple pizza party. As an event organiser both at workplace and amongst societies I have found out that a secret to increase attendance to any event is food!
If someone asks you how screening movies is contributing to awareness, don’t worry, throw in a Security Quiz at the end of the movie. This would even suffice your audit requirements too. You can also talk about some cool software and hardware gadgets that can safeguard both professional and personal lives too from a cyber security perspective. Some are listed down in the article.
Here are some suggestions:
Movies:
Snowden
Snowden is a biographical thriller released in 2016 and based on the life and events surrounding Edward Snowden’s whistle blowing. Snowden is considered a hero by some, and a traitor by others. No matter what happened, the epic story of why he did it, what he risked, and how he pulled it off makes for one of the most compelling films. This movie provides great insights into the inner workings of surveillance programs at the Nation-State level and what it means to the privacy of the general public. While I hate to reference it, the movie also showcases the risks of insider threats.
LINK: https://www.imdb.com/title/tt3774114
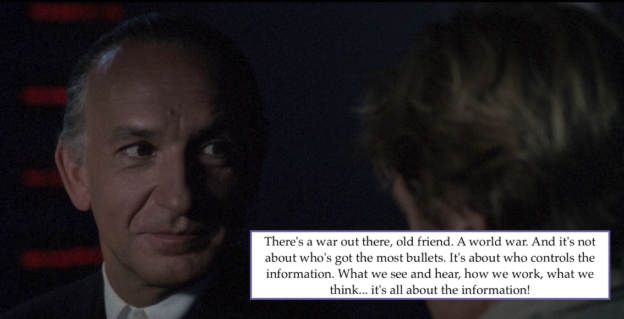
Sneakers:
If you are a pentester or red team engineer and wanted to explain what you do for a living to your friends and family, then this is it, apart from some useful security tips and geek stuff. For a movie released in 1992, the plot had cutting-edge hacking and pentesting skills way ahea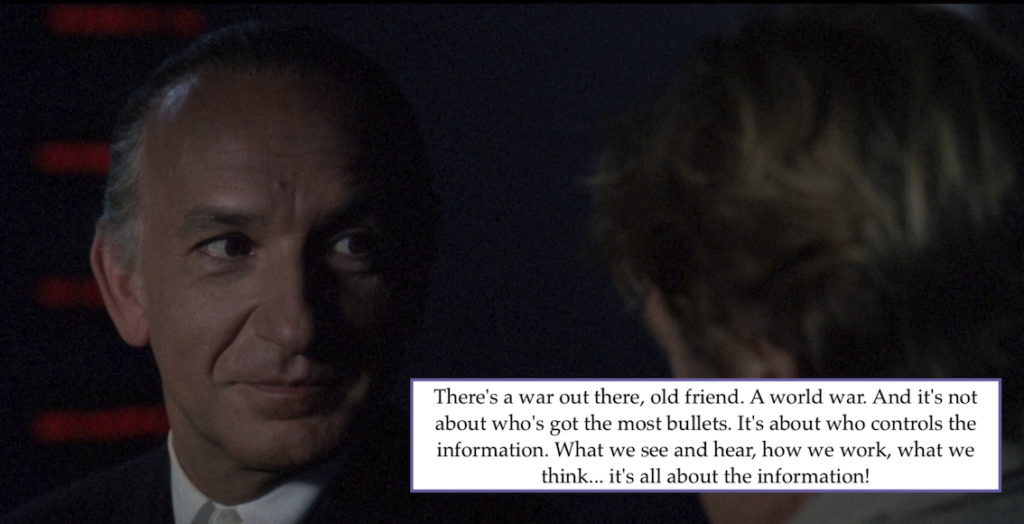 d of its time including some cool social engineering tricks. A team of penetration testers become embroiled in a turf war between Government agencies and rogue hackers over a device that can crack all encryption (quantum cryptography anyone?). This movie has some prophecies too! Considering we have had multiple whistle blowing incidents in the recent past, as a security practitioner both the above movies emphasis one thing: Do the right things or walk away. CISOs are you listening ?
d of its time including some cool social engineering tricks. A team of penetration testers become embroiled in a turf war between Government agencies and rogue hackers over a device that can crack all encryption (quantum cryptography anyone?). This movie has some prophecies too! Considering we have had multiple whistle blowing incidents in the recent past, as a security practitioner both the above movies emphasis one thing: Do the right things or walk away. CISOs are you listening ?
Wargames
Have you wondered about the worst case scenarios around automation, or lack of segmentation between your dev and production environments? Or even the implication of a red team exercise going wrong and causing downtime to your production environments? This movie has many of it…
This movie was released in 1983 and starred Mathew Broderick as a lead character. A young computer whiz kid accidentally connects into a top secret super-computer which has complete control over the U.S. nuclear arsenal. It challenges him to a game between America and Russia, and he innocently starts the countdown to World War 3
LINK: https://www.justwatch.com/us/movie/wargames
The Matrix
If there was ever a movie that brought to life the concept of hacking, simulation through its characters, that has to be matrix. There is a hacker, there’s a character called cipher. How do machines get access to the rebel network? they compromise cipher 😉 Matrix is a story of a computer hacker who joins a group of underground rebels fighting the vast and powerful computers that have taken over the earth. This movie was released in 1999 and also features a very popular security tool (let me know in the comments)
LINK: https://www.justwatch.com/us/movie/the-matrix
Mr. Robot
This is an award-winning web series released in 2015 and is now in its seventh season. This is a story of a hacker by the name of Elliot Alderson. He is a brilliant introverted young programmer who works as a cyber-security engineer by day and a vigilante hacker by night. He and his group are out to erase the credit history for all.
This series features all the things that are talked about in the world of cyber security: Tactics, Techniques, and Procedures (TTPs). You name it and the series has it including Social Engineering, using Raspberry Pis to discretely connect to networks, throwing malware loaded USB sticks in parking lots and lot more
LINK: https://www.imdb.com/title/tt4158110/?ref_=ttmi_tt
Gultoo
Do you remember this Apple’s Privacy ad which created quite a stir when released on how we are tracked? That ad has a stark resemblance to a song in this movie called Gultoo, released a couple of years earlier. This underrated Kannada movie captures the journey of a hacker who is a part-time instructor in a computer training institute and the skills he uses capture the biometrics of a colleague and use it to find real identity, or use shoulder surfing and snooping in coffee shops to access passwords. This is a great movie that appeals to the younger generation and since it is made in India, folks here may be able to relate to it.
https://www.imdb.com/video/vi3980900633/?ref_=ext_shr_lnk
Books:
Many companies that I know of have a tie up with library chains where books are delivered to your offices. Here are some good books that talk about various aspects of cybersecurity and are fun to read:
Cult of the Dead Cow
Cult of the Dead Cow is the tale of the oldest, respected, and most famous American hacking group of all time popularly called Cult of the Dead Cow or cDc. This book chronicles the journey of Hacker Culture, the origin of various conferences like DefCon, Blackhat. How hacktivism started, the journey of various security tools like l0phtcrack, nessus, etc.,
Many of the hackers in this group have become well-known names in the technology and security field like Peiter Zatko and Beto O’ Rourke. Peiter Zatko, popularly known as Mudge was in the news recently as the whistle-blower of improper security practices at Twitter. He had earlier served as Head of Security at Twitter. Beto O’Rourke is former Texas Congressman and was a presidential candidate LINK
Permanent Record
Although this is an auto-biography on Edward Snowden, this book provides great insights into the inner workings of surveillance programs at the Nation-State level and what it means to the privacy of the general public. LINK
Cuckoo’s Egg:
Who doesn’t like mystery and thriller novels? This is a true story written by Cliff Stoll in1989. Cliff Stoll was an astronomer turned systems manager at Lawrence Berkeley Lab. An accounting error alerted him to the presence of an unauthorized user on his system. Stoll began a one-man hunt of his own: spying on the spy. It was a dangerous game of deception, broken codes, satellites, and missile bases. His hunt finally gained the attention of the CIA…and ultimately trapped an international spy ring fuelled by cash, cocaine, and the KGB.
Gadgets
You can talk about the benefits of gadgets like Privacy filters, webcam stickers, Hardware MFA keys that are phish-resistant etc.,
A gadget like Privacy Filter narrows the viewing angles and prevents shoulder surfing or snooping by others. This is a great addition for the sales and marketing teams and CXOs who are on the road and working out of cafes, airports, and other crowded places.
We have recently learned from the Uber hack about the MFA push notifications alert, which led to fatigue and employee selecting Yes after a barrage of requests. This is a worrying aspect as I have encountered a couple of similar attempts and I dread what if I pressed Yes or clicked on checkmark instead of an X!
This is where a hardware MFA token comes to the rescue. It is been published that hardware MFA tokens (those that comply to the FIDO framework) are phish-resistant. You can popularise these in your offices instead of traditional soft MFAs
I think password managers are still the most underrated tool when it comes to cyber security. We still have not transitioned from “remembering your password” to “passwords are not meant for remembering” mode.
Use the password manager in conjunction with a key or a token and then all you need to remember is just one password and the rest should be in a password manager on system or a browser.
How are you tackling the awareness fatigue of your employees? Please do comment and share your thoughts.